Access Gravity™: Not All Permissions Are Created Equal
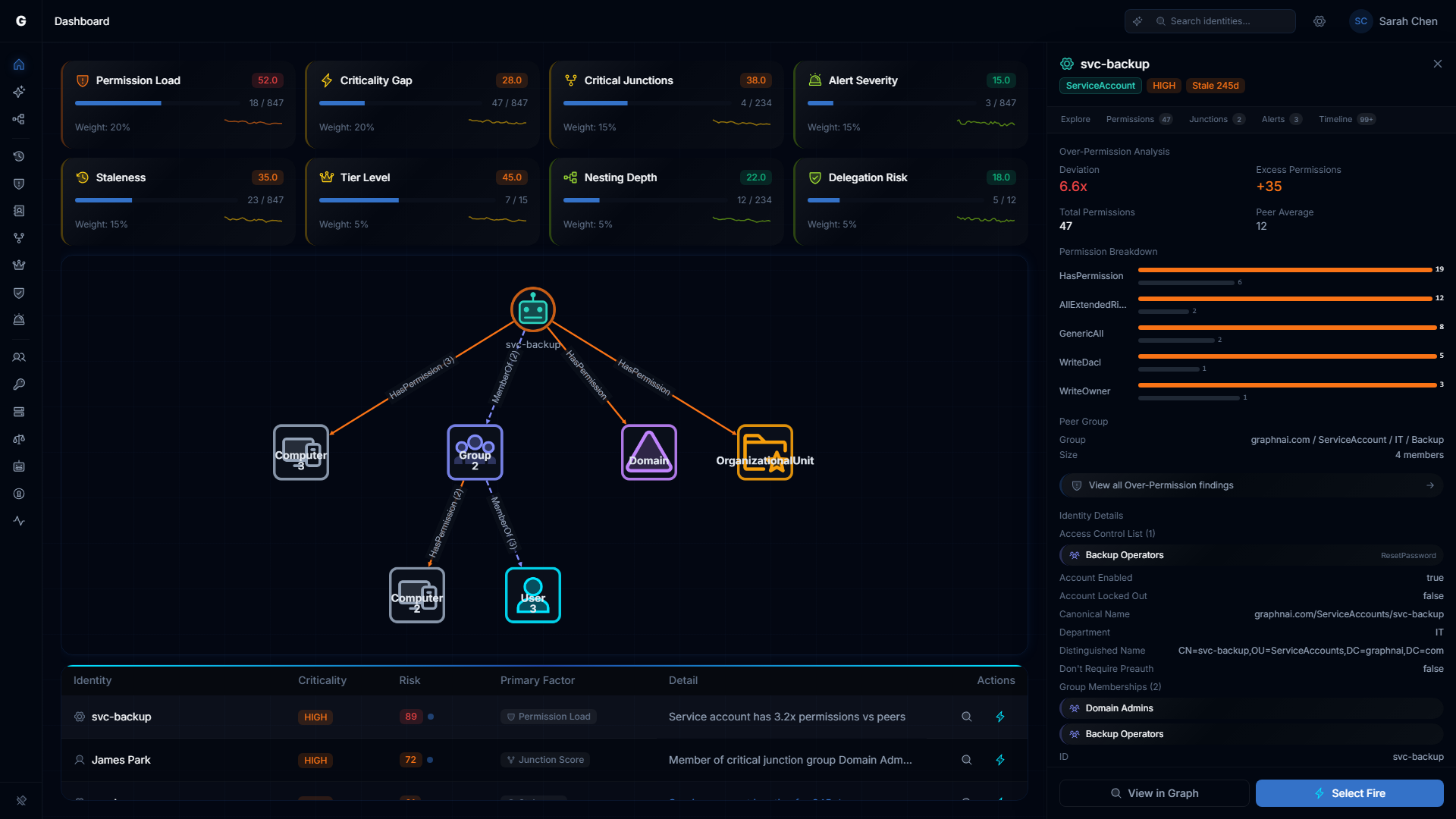
Eight risk dimensions from edge weighting to delegation posture. The biggest risks always surface first.
A benign inherited permission on a public attribute. Full control over a GPO linked to your Domain Controllers OU. Count-based tools treat those as the same thing: one permission each. That's insane.
We built Access Gravity because permission counting is broken. Some tools categorize permissions by type, which helps. Most IGA and posture tools still just count them. Ten permissions? High risk. Two permissions? Low risk. What if those two permissions grant full control over a GPO that configures every domain controller, and the ten are harmless inherited entries on non-sensitive objects? The count tells you nothing. The weight tells you everything.

How It Works
Every permission type gets a severity weight based on what attackers actually do with it. Full control, password reset, security descriptor modification. Those are the keys to the kingdom. They get heavy weights. Benign inherited entries on non-sensitive attributes? Near zero.
When Identity Folding consolidates edges, Access Gravity computes a composite score for each relationship. A single edge with full control and group modification scores higher than an edge loaded with harmless inherited permissions. That's the foundation. But edge-level weighting is just the first layer.
Beyond Edge Weighting: Eight Risk Factors
Edge severity tells you which relationships are dangerous. It doesn't tell you which identities to fix first. For that, you need identity-level risk scoring across multiple dimensions. Access Gravity rolls eight factors into a composite Identity Risk Score:
Permission Load compares each identity against its peers. Same domain, same type, same department. If a service account has 5x the severity-weighted permissions of similar accounts, that's a finding. Not because 5x is a magic number, but because it means something about this identity is different from everything around it.
Criticality Gap is the asymmetric scoring that changes everything. A low-priority helpdesk account with access to a critical domain controller scores higher than a domain admin accessing the same system. The gap between source and target criticality is the risk, not the absolute level. A critical identity accessing critical resources is expected. A low-tier identity doing the same thing is the problem.
Critical Junctions flags identities that bridge otherwise-separated security boundaries. If removing one account would disconnect two parts of your access graph, that account is a single point of failure and a single point of compromise.
Alert Severity pulls from the ITDR detection engine. Active brute force attempts, password spray, Kerberoasting, DCSync. An identity under active attack gets prioritized over one with static misconfigurations.
Staleness measures how long since the identity was last active. Different thresholds for different types: 90 days for users, 30 for computers, 180 for service accounts. Stale accounts with powerful permissions are the lowest-hanging fruit for attackers.
Tier Level reflects position in the Enterprise Access Model. Tier-0 assets carry the highest weight because compromise at that level means game over.
Nesting Depth catches the invisible privilege chains. Six levels of group nesting between a user and Domain Admins? Nobody auditing group memberships manually will find that. Access Gravity does.
Delegation Risk is the blind spot no other tool scores. Unconstrained Kerberos delegation. Cross-tier delegation paths. Inherited custom ACEs that grant unexpected control. Delegation is the number one misconfiguration in enterprise AD, and it's the one most tools ignore entirely.
Key Benefits
- Eight risk factors. Not one arbitrary score. Each dimension is independently weighted so nothing hides behind a blended average.
- Full control over a Domain Controllers GPO will never hide behind a wall of harmless low-severity entries.
- Criticality Gap scoring means a low-priority identity accessing a Tier-0 asset always surfaces first. The asymmetry is the point.
- Delegation Risk catches the blind spots other tools miss entirely: unconstrained delegation, cross-tier access paths, inherited custom ACEs.
- Peer-group comparison surfaces the outliers. Same role, same department, but 5x the permissions? That's your finding.
- The Risk Posture Dashboard gives you one number for your whole environment. Track it over time. Drill into any factor.
- Remediation priority becomes a number, not a meeting. The data decides what gets fixed first.
See it in action on the Risk Posture Dashboard. For delegation analysis details, see the Delegation Posture guide.