Attack Surface Management
Visualize the blast radius, then fix it safely. Graph-based attack path analysis with simulation and guided remediation.
Your identity attack surface isn't a list of misconfigurations. It's a graph. Permissions chain through group memberships, delegation paths cross security boundaries, and a single compromised service account can reach Tier-0 through paths nobody mapped manually. You need to see the graph to defend it.
GraphnAI builds a full identity graph from your AD and Entra ID environments, then analyzes it for the structural weaknesses attackers actually exploit. Not theoretical paths from a textbook. Real attack surfaces shaped by your specific permission topology, group nesting, and delegation chains.
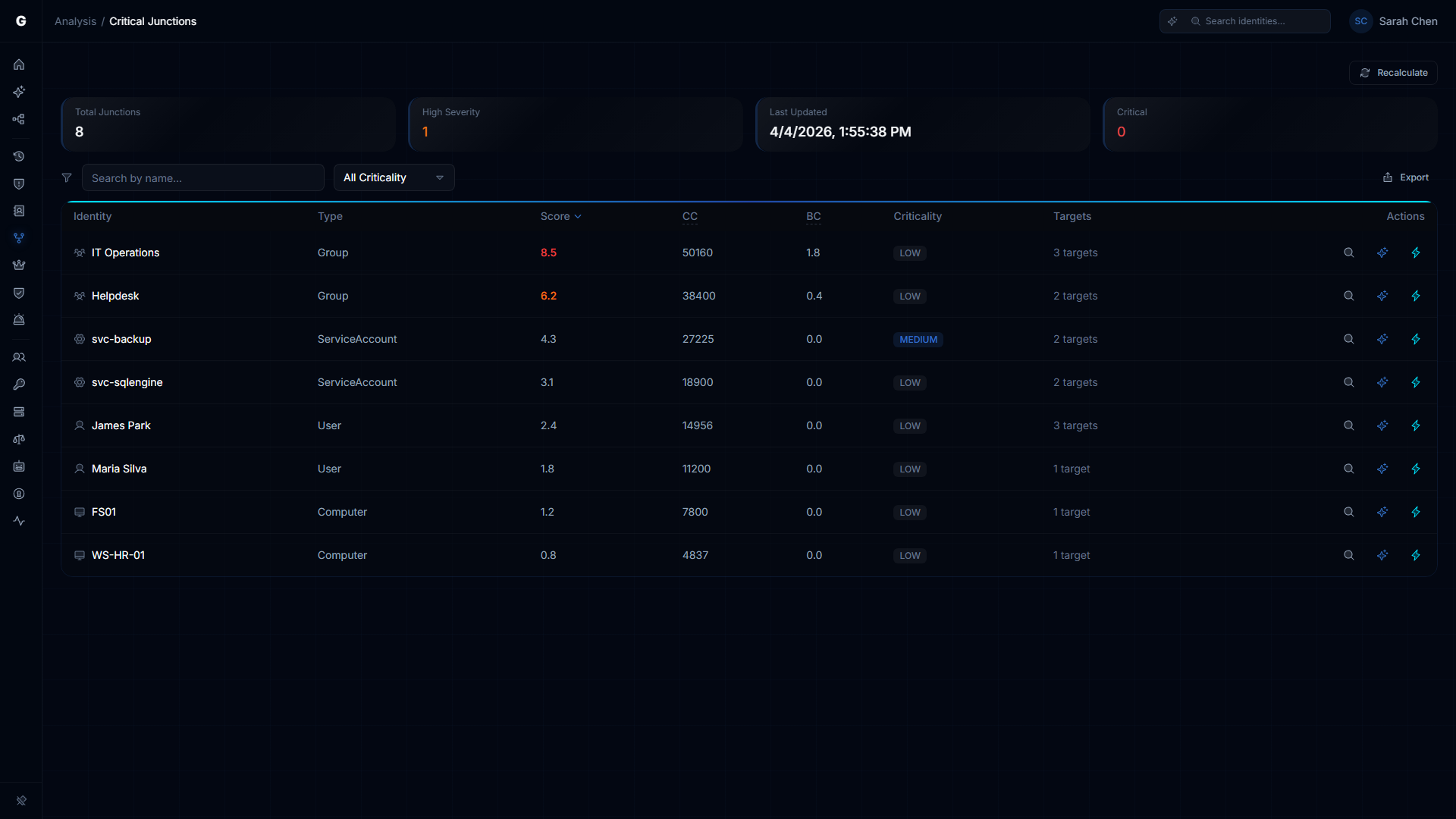
Critical Junction Analysis
A critical junction is an identity that bridges otherwise-separated parts of the access graph. Remove it, and two security domains disconnect. Compromise it, and an attacker crosses a boundary in a single hop. These are the identities that matter most, and they're invisible in permission lists.
GraphnAI scores every junction by the number of unique targets reachable through it, the criticality of those targets, and the severity of the permissions involved. A group that bridges 200 workstations scores differently from one that bridges a single domain controller. Both are junctions. Only one is critical.
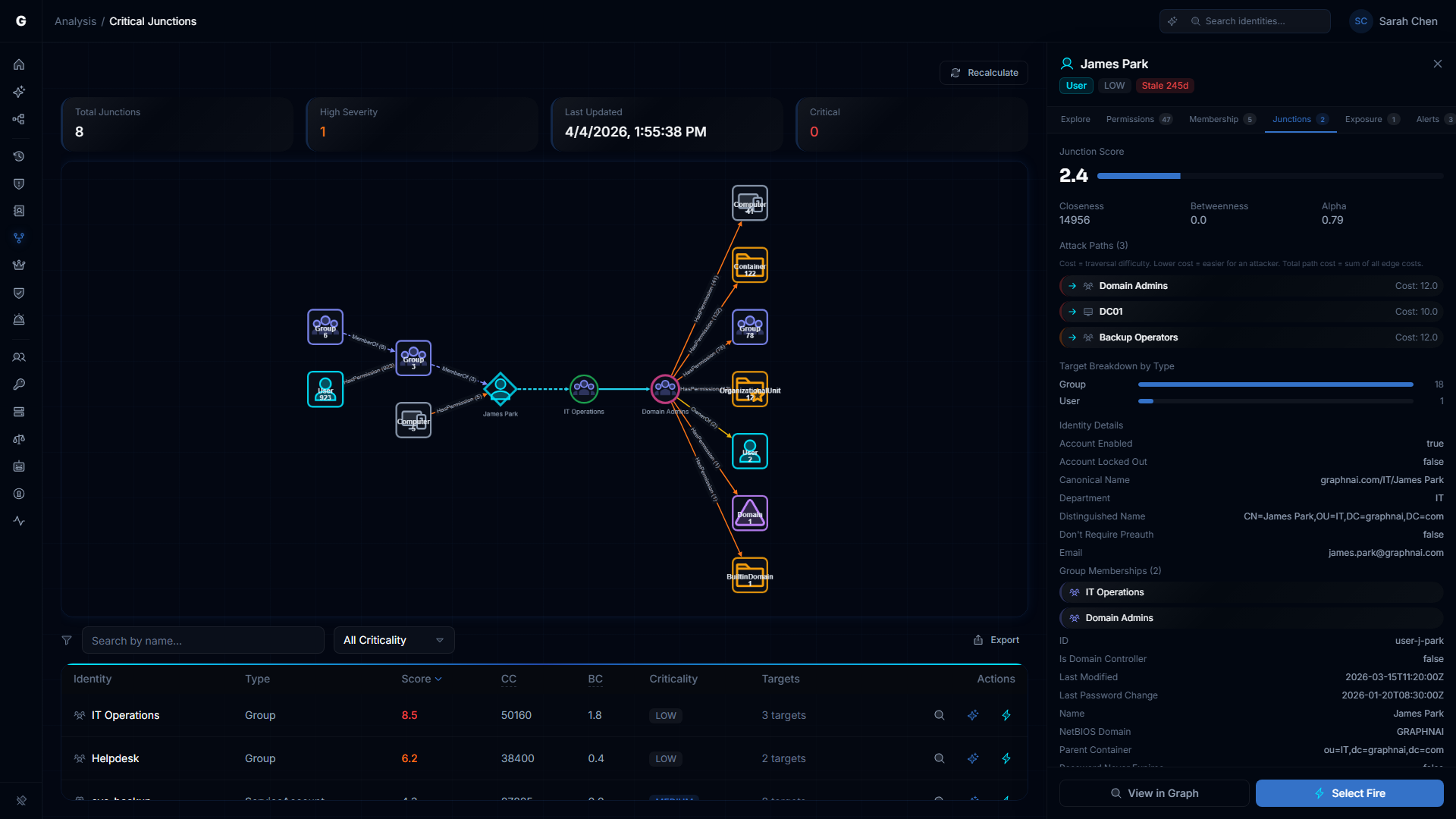
Attack Path Visualization
The junction detail view renders the full attack path graph. The junction node sits at the center. Fan-out shows every target reachable through it, grouped by type. Fan-in shows every identity that can reach the junction. You see the complete blast radius of compromising that single identity.
Edge coloring reflects fidelity tier. Green paths are validated by telemetry. Amber paths are constrained by policy. Gray dashed paths are theoretical. When you can see which paths are actually live, you stop wasting time on theoretical attack chains.
Asset Criticality and Blast Radius
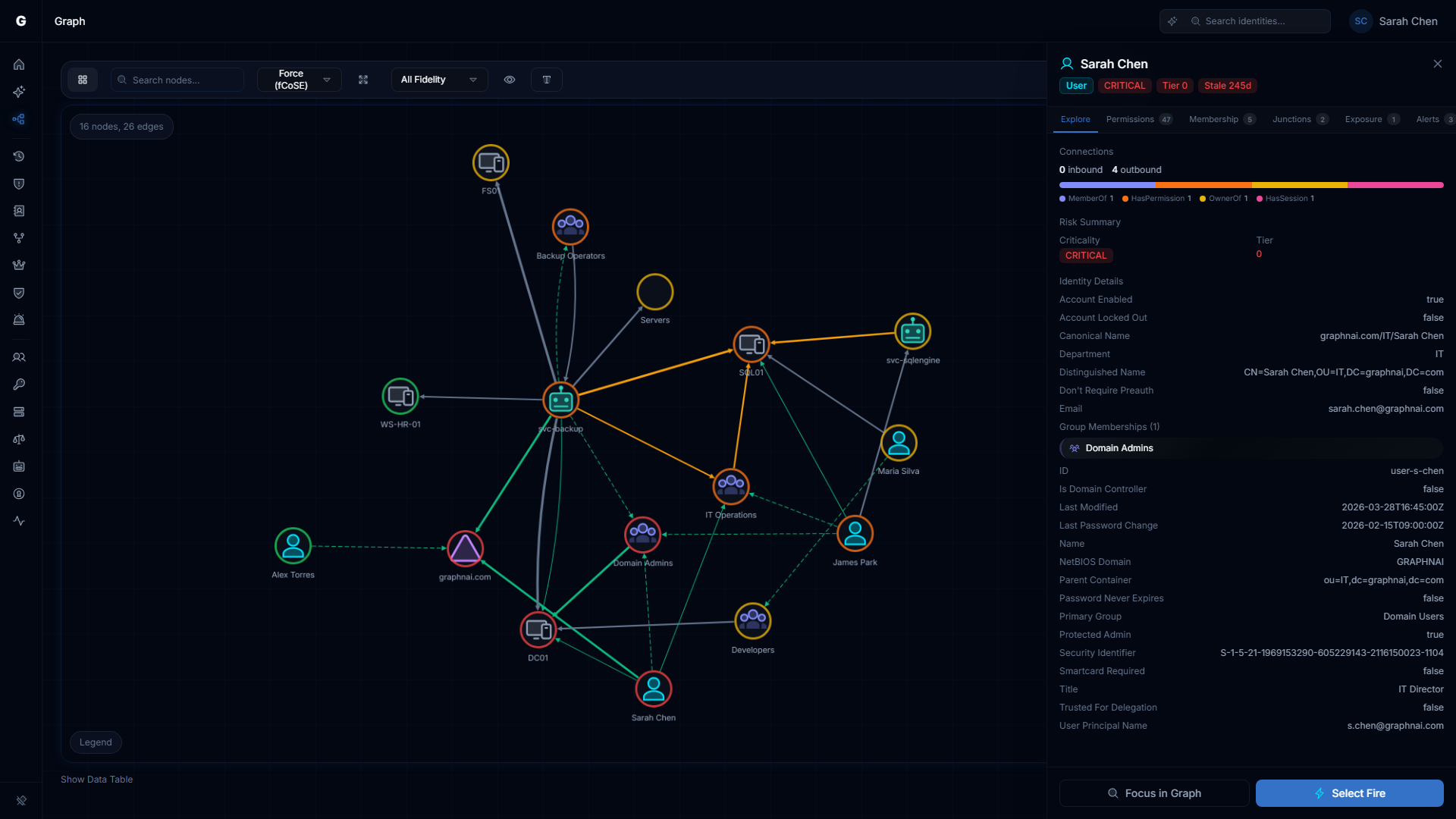
Not every asset matters equally. GraphnAI classifies identities by criticality (Critical, High, Medium, Low) using both system rules and custom overrides. Domain controllers, Tier-0 groups, and certificate authorities are automatically classified. You add the business context: that SQL server running payroll is Critical even if AD doesn't know it.
Every analysis layers criticality into the scoring. A junction reaching 50 Low-criticality workstations scores differently from one reaching 3 Critical domain controllers. The graph visualization shows criticality through border coloring, so dangerous paths are immediately visible.
Attack Surface Management Capabilities
- Interactive identity graph with Tiered Fidelity coloring, full-text search, and node property detail
- Critical junction detection scoring reach, target criticality, and permission severity per junction identity
- Blast-radius simulation via the Differential State Engine. See who loses access before you touch production.
- Asset criticality engine with system rules (AdminSDHolder, KRBTGT, DC$) and custom overrides for business context
- Select Fire remediation workflow: Preview the finding, simulate the change, then decide Safe/Semi-Auto/Full-Auto
- Identity Folding consolidates millions of raw permissions into readable composite edges. 10-100x noise reduction.
Explore the details: Critical Junctions · Graph Explorer · Asset Criticality · Identity Graph · Select Fire