Identity Threat Detection & Response
Catch active threats, not just stale configs. Real-time detection with identity-aware context and full investigation timeline.
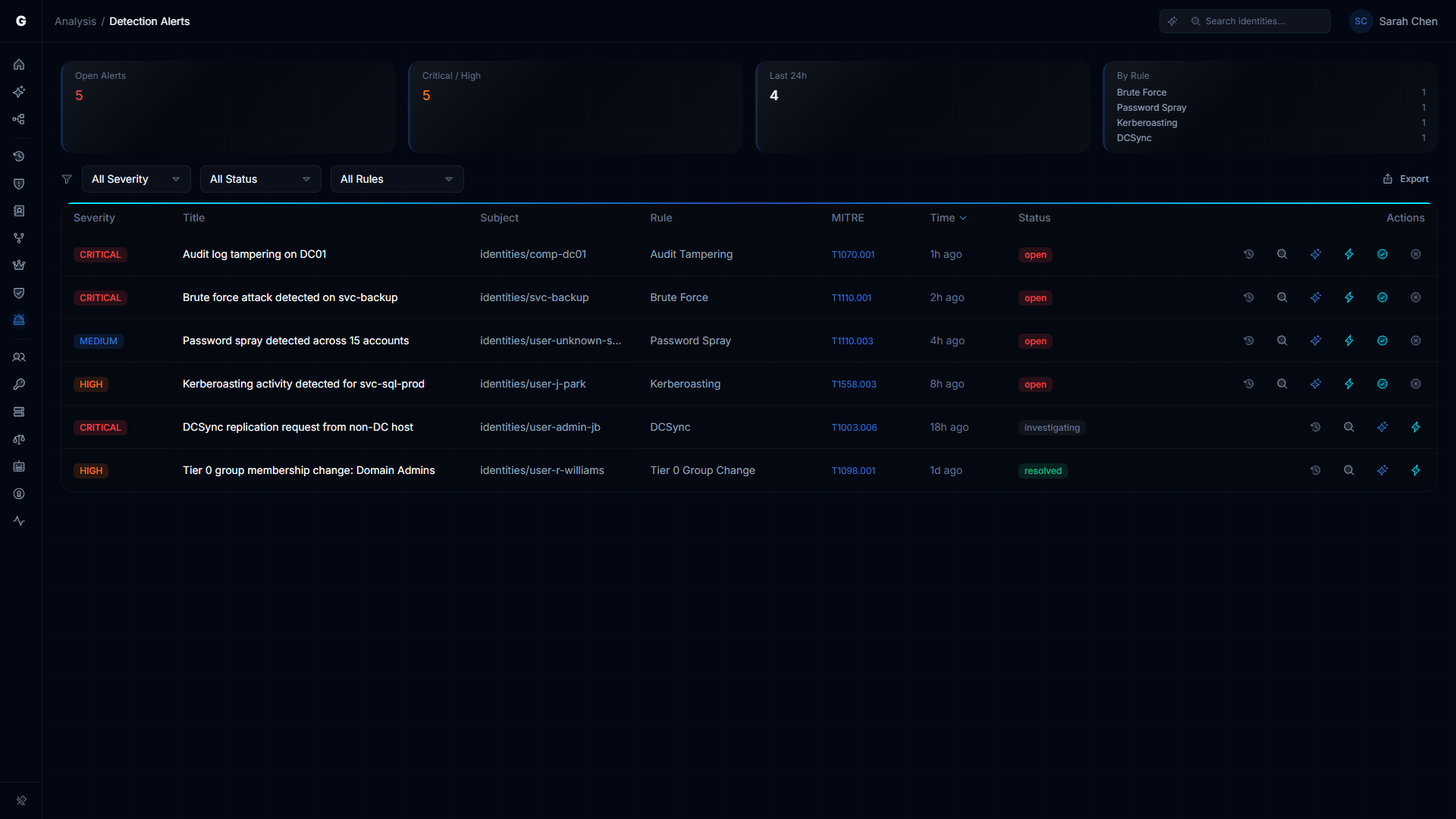
Posture management finds what's misconfigured. Attack surface analysis shows what's exploitable. Neither tells you what's being exploited right now. ITDR closes that gap. When an attacker is actively spraying passwords, Kerberoasting service accounts, or replicating your directory, you need to know in minutes, not during the next audit.
GraphnAI ingests security event telemetry from your domain controllers and Entra ID audit logs, normalizes it into a unified event model, and runs detection rules against the stream. When a detection fires, it's not just an alert. It's an alert with full identity context: who this identity is, what they have access to, how they compare to their peers, and what the blast radius would be if they're compromised.
Detection Rules
Six detection rules cover the identity attacks that matter most. Brute force authentication against individual accounts. Password spray campaigns hitting multiple accounts with the same password. Kerberoasting attempts requesting TGS tickets for service accounts with SPNs. DCSync attacks replicating directory data from non-DC sources. Tier-0 group membership changes that could grant immediate domain control. Audit log tampering that covers an attacker's tracks.
Each detection includes MITRE ATT&CK mapping, severity classification, and the specific evidence that triggered it. Not a probability score. The actual events.
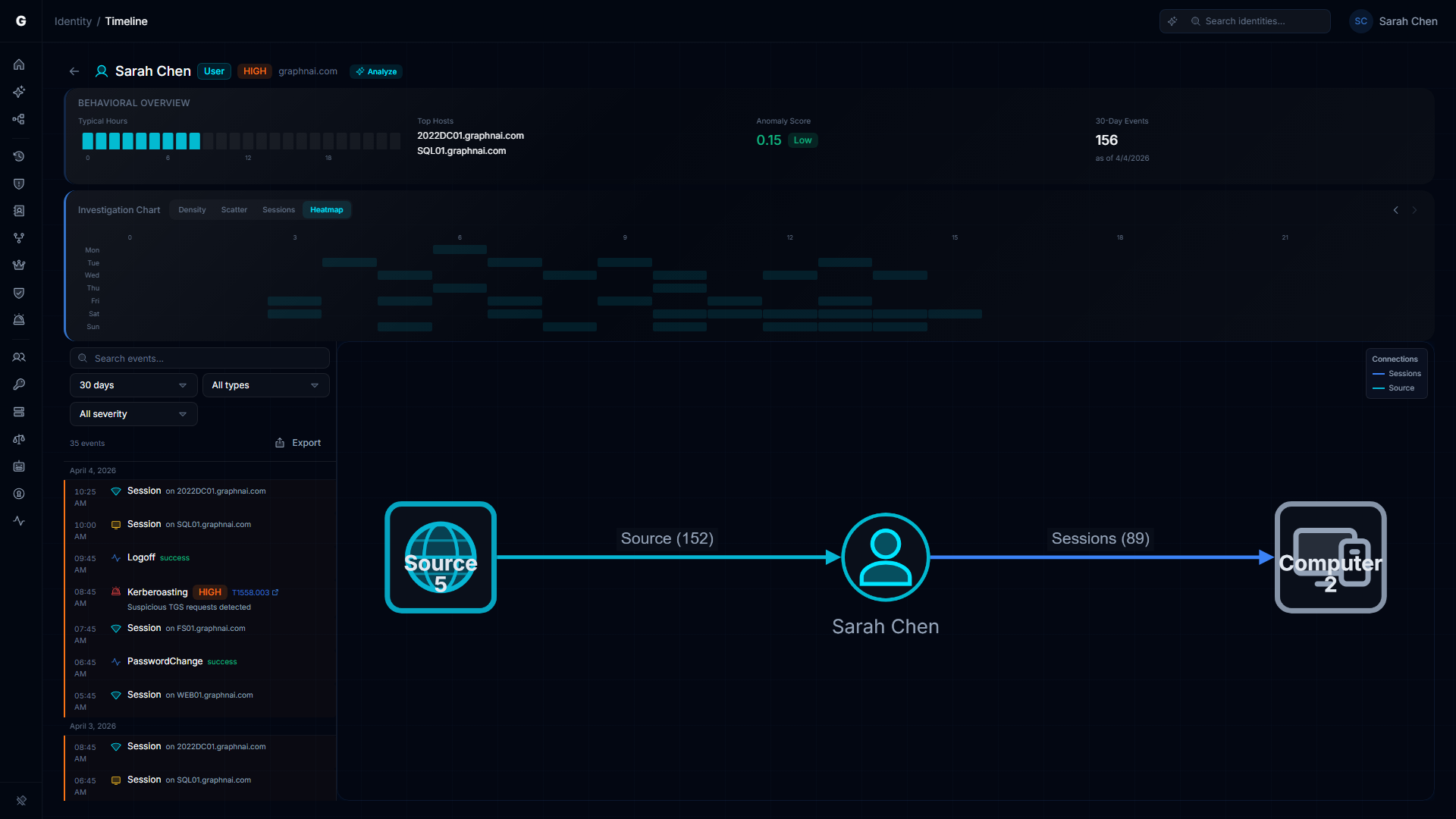
Identity Investigation Timeline
When a detection fires, you need the full story. The identity timeline shows every authentication event, session, privilege use, directory access, and alert for any identity across a configurable time window. Sessions show which hosts the identity authenticated to, which protocols were used, and whether the logon succeeded or failed.
The timeline is chronological, but raw event logs aren't how you find patterns. The activity heatmap visualizes authentication density over time. A service account that normally authenticates at 2 AM during batch windows suddenly showing up at 3 PM? The heatmap makes it obvious. The scatter plot correlates event types across time so you can see when normal behavior diverges.

Behavioral Analysis
The activity heatmap builds a behavioral fingerprint for every identity. Day-of-week and hour-of-day authentication patterns emerge naturally from the telemetry. When an identity deviates from its established pattern, the heatmap makes it immediately visible without requiring manual baseline configuration.
This behavioral context feeds back into the posture model. An identity with validated sessions (Tier 3 fidelity) is a confirmed active access path, not a theoretical one. Telemetry-validated edges promote automatically in the identity graph, sharpening the risk posture over time.
Threat Detection Capabilities
- Six detection rules: brute force, password spray, Kerberoasting, DCSync, Tier-0 group change, audit log tampering
- MITRE ATT&CK mapping on every detection with specific technique IDs and evidence
- Identity investigation timeline with chronological event stream, session tracking, and protocol detail
- Activity heatmap for behavioral analysis: authentication density by day-of-week and hour-of-day
- Telemetry-driven fidelity promotion: observed sessions validate theoretical access paths automatically
- Alert severity feeds into the Risk Posture Dashboard. Active threats elevate identity risk scoring in real time.
Explore the details: Detection Alerts · Identity Timeline · ITDR Detection · Telemetry Pipeline · Telemetry Enrichment